You Escaped the System. Now What?
In this article:
What would you do if your access to money could be switched off, not because you broke the law, but because you made the wrong political decision?
That’s no longer theoretical.

In November 2024, the International Criminal Court (ICC) issued arrest warrants for Benjamin Netanyahu and former Defence Minister Yoav Gallant, alleging war crimes and crimes against humanity in Gaza. The decision was approved by a panel of judges, including French judge Nicolas Gouyou, who has since become a case study in how the financial system actually works.
The financial consequences did not come immediately. They came later.
In 2025, the United States imposed sanctions on several ICC officials involved in the case. And by 2026, the real-world effects of those sanctions had become visible.
His cards stopped working. Visa. Mastercard. You name it.
Because nothing says “neutral payment infrastructure” like turning a sitting international judge into a financial ghost overnight. Welcome to the real financial system: a state-controlled weapon that governments point at anyone who steps out of line.
No ability to make everyday purchases. No access to services most people take for granted, from online shopping to basic bookings.
In his own words, he was “treated like a criminal” , sanctioned alongside terrorists and drug cartels, despite acting in a judicial capacity. Remember, there was no criminal trial against him, no charge directed at his finances, and little opportunity to challenge the restrictions before they took effect.

Call it what it is: the financial arm of the state. A weaponized monopoly on money that lets governments and their obedient banking partners paralyze anyone who dares step out of line. And it doesn’t need to confiscate your money anymore.
Why bother confiscating it…when they can simply make it unusable?
If that can happen to a judge operating at the highest level of international law, it is worth asking what happens further down the chain.
Because the direction of travel is not towards less control, it is towards more.
Central banks are actively developing digital currencies, so-called CBDCs, where money exists entirely within centrally managed systems. In such a framework, transactions are not just processed; they are recorded and monitored by design, with the ability to restrict transactions directly at the infrastructure level.
In other words: programmable money that lets governments and their financial partners turn your wallet into a surveillance device and a remote-control switch at the same time.
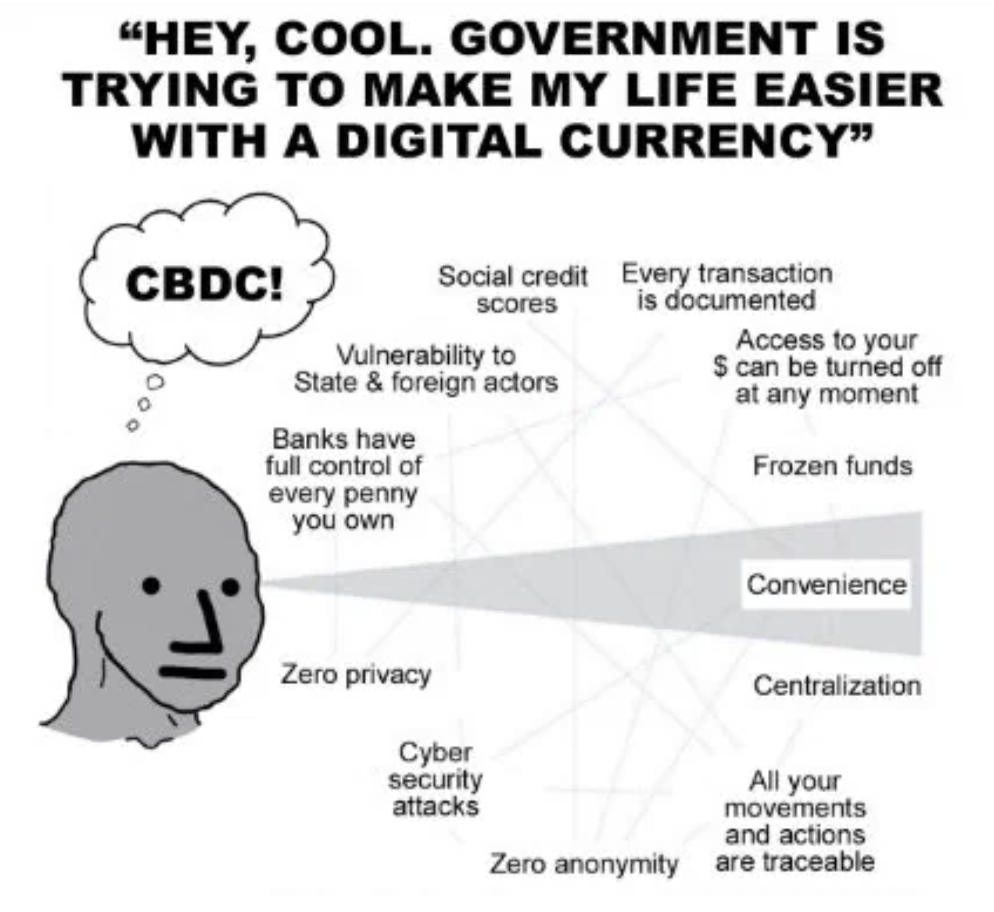
And once that capability exists, the question is no longer whether it can be used.
Only when.
Stepping Outside the System
Here’s the uncomfortable truth most people still refuse to see: you don’t control your money.
The government-banking cartel does. Not in some abstract, philosophical sense, but in a very real, operational one, through institutions that process it, the networks that move it, and our beloved politicians who ultimately define the rules.
As long as you stay a good little compliant citizen and keep your head down, everything functions as expected.
The moment your interests no longer align with theirs? The mask comes off. Suddenly, you discover that your “money” was never yours. Instead, it was just a temporary permission slip issued by the government-banking complex, revocable the moment your interests diverge from theirs.
For a long time, that trade-off was unavoidable. There was no meaningful way to hold or transfer value without relying on the same system that could restrict it. You could move between banks, jurisdictions, or providers, but you never really left the structure itself. You were simply navigating within it.
Bitcoin doesn’t operate within that framework. It doesn’t depend on payment networks, and it doesn’t rely on institutions to process or validate transactions. Its rules are not adjusted in response to political pressure or regulatory alignment.
Stepping outside the system doesn’t just remove constraints; it also hands responsibility back to you. The system no longer carries it on your behalf.
In Bitcoin, there’s no built-in safety net, no reset if something goes wrong, and no institution stepping in to undo a mistake. For the first time in your life, you’re no longer renting access to your own wealth from a cartel that can switch it off whenever it suits them.
But you don’t get that freedom without taking ownership of the consequences.
Most People Stop Too Early
This is the part where most people pat themselves on the back and completely miss the point.
They finally wake up, see the fiat clown show for what it is, go through the journey, understand why Bitcoin matters, and take what feels like decisive action. They buy a hardware wallet, generate a seed phrase, and move their coins off an exchange.
At that point, there’s a sense of completion like a box has been ticked. Mission accomplished. “I’m sovereign now”. Self-custody solves a very specific problem: it removes the custodian. It ensures that your Bitcoin is no longer held inside an institution that can freeze it, restrict it, or otherwise interfere with it.

That’s amazing progress.
But it doesn’t magically secure the rest of your life.
Because the moment you remove the intermediary, the responsibility for the entire environment shifts. It moves to your devices, your accounts, your backups, your behaviour, and the way your overall setup has been designed. You didn’t just become your own bank, you also became head of security.
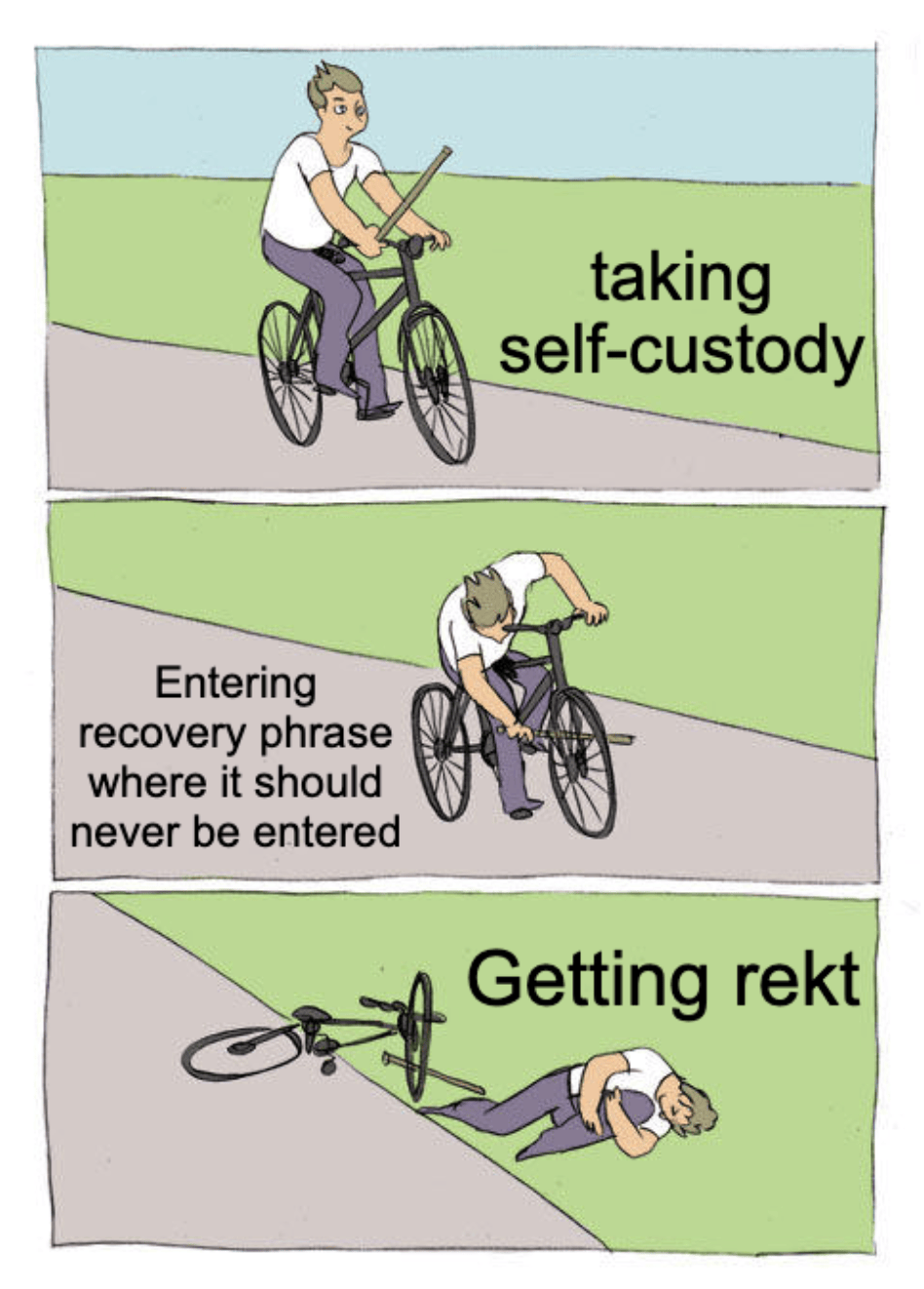
This is the part most people underestimate. If your setup is half-baked or thrown together, you’ve got a real problem.

They assume the primary risk was the exchange, and once that’s removed, they assume the problem itself has been solved. In reality, the risk has simply changed form. Self-custody protects you from custodians. It doesn’t protect you from a poorly structured setup, unnecessary exposure, or avoidable operational mistakes.
Securing your Bitcoin is not the same as securing your Bitcoin setup.
And until you internalize that uncomfortable truth, it’s ridiculously easy to trade the false sense of security the banks sold you… for an even more dangerous false sense of security that you sold yourself.
Where the Real Risk Actually Sits
So what actually happens once you’ve taken custody?
The hard part is over, right? No, in reality, that’s usually where the real security work begins, because the weak point is no longer some third-party custodian.
It’s everything around you. Your phone, your laptop, your email, your backups, your habits, your visibility, and the amount of information you leak without even realizing it.
And that matters because most people don’t get “hacked” in the cinematic sense. They get exposed through something much more ordinary: a recovery phrase entered where it should never have been entered, a compromised email account, malware that swaps addresses, an insecure backup, or a setup held together by half-understood advice from ten different YouTube videos.
So if you want to avoid getting wrecked, there are four practical principles that matter far more than sounding technical.
- Treat your seed phrase like a live grenade. It should never be typed into a browser, pasted into a note-taking app, photographed, stored casually in the cloud, or handed to anyone claiming to be “support.” Any request for your recovery phrase is almost certainly a theft attempt. That rule alone eliminates a huge percentage of the stupid losses people call “hacks.”
- Separate spending money from serious money. Not everything needs to live behind the exact same setup. A smaller, more accessible wallet for day-to-day use and a more hardened structure for long-term savings is often far more sensible than pretending one wallet should do everything. That is also why singlesig is not the only setup. For some people, a well-designed singlesig arrangement is entirely adequate. For others, adding a passphrase or moving to multisig makes far more sense, especially as the amount grows and the consequences of a single point of failure become less acceptable. Convenience and resilience don’t have to be on the same layer.
- Build for coercion, not just for theft. This is where a decoy wallet and passphrase can matter. Passphrases can be useful in coercive scenarios because they allow distinct wallets and plausible deniability. That doesn’t make you invincible, and it is not something to improvise casually, but it does recognise a basic reality: if somebody can put pressure on you physically, your security model cannot begin and end with “I wrote down 24 words.” France has already shown what happens when criminals start targeting identifiable Bitcoin holders.

- Reduce your visibility. A great security improvement is not another gadget but becoming less legible as a target. Don’t advertise holdings. Don’t post screenshots. Don’t attach your identity to balances, devices, addresses, or habits any more than necessary. The less obvious you are, the harder you are to target.

And the reassuring part is that none of this requires you to become an IT professional. It requires structure.
Not hours of scattered research, not piecing things together from forums and guesswork. Just a setup that’s been thought through properly and aligned with your circumstances, ideally with guidance from professionals who’ve already done it many times before.
Doing It Properly
At this point, most people feel two things at once.
Clarity and a slight discomfort. Clarity, because the path is obvious. Discomfort, because they realise they might not have done it properly.
That’s normal. Most people lose their funds or get compromised because their setup was never designed properly in the first place.
What we do at The Bitcoin Way is simple: we help you build this properly. Not by turning you into a security engineer. But by guiding you through the process, so that you understand what you’re doing and why it works.
- Self-custody: set up correctly, with clarity and confidence.
- Personal cybersecurity: so your devices, accounts, and data don’t become the weak link.
- Reducing exposure: so you’re not making yourself an easy target without realising it.
- Ongoing support and training: so your setup continues to make sense as your situation evolves.
