This Again? A Clearer Look at Quantum and Bitcoin

In this article:
How many times are we going to fall for this?
Every few months, like clockwork, a familiar headline makes the rounds: “Quantum computing could break Bitcoin”.
It spreads like wildfire because it sounds smart, technical, and just plausible enough to scare people. And of course, it comes with that delicious hint that maybe, just maybe, something fundamental may have changed and the Bitcoin dream is finally over.
So here we are again: another round of “Bitcoin is doomed” headlines designed to make you doubt the one asset that doesn’t need permission from the clowns who print money and lie about inflation.
Each cycle brings a new paper, a new estimate, or a new milestone, often presented in a way that makes the timeline feel closer than before. But if you’ve been in this space for more than five minutes, you’ll recognise the script immediately.
Variations of this concern go back to the early days of Bitcoin itself. Even Satoshi himself addressed this exact concern back in 2010, calmly pointing out that if a cryptographic primitive ever weakened, the network could adapt and transition in an orderly way.
That doesn’t make the concern irrelevant. But it does mean it’s worth stepping back before reacting to the headline itself.

The Basis Of The Concern
To understand what all the noise is actually about, it helps to go back to the basics.
We’ve covered this in more detail here, but the core idea is relatively straightforward.
Bitcoin relies on a cryptographic system called Elliptic Curve Digital Signature Algorithm (ECDSA) to prove ownership of funds. When you sign a transaction, you use a private key to produce a signature that can be verified against a public key.

You can think of it like a padlock. The public key is the lock you share with the world. The private key is the only key that can open it.
Anyone can see the lock and verify that it works. But they can’t recreate the private key just by looking at it. The security of that system depends on the difficulty of solving the ECDSA, a problem that classical computers cannot feasibly reverse.

But quantum computers work differently. Instead of normal bits that are either 0 or 1, they use qubits that can be in multiple states at once and can become entangled with each other. This lets them explore many possibilities in parallel rather than one after another.
Shor’s algorithm is a type of algorithm that only works on a quantum computer. It is specifically designed to solve certain mathematical problems, like factoring large numbers or finding discrete logarithms, much faster than any known classical method.
It does this by using quantum properties to uncover patterns in numbers that classical computers would struggle to find in a realistic amount of time. Because modern cryptography relies on these problems being hard to solve, Shor’s algorithm means that a sufficiently powerful quantum computer could break systems like RSA or elliptic curve cryptography by deriving private keys from public keys.
That’s the basis of the concern.
It’s also worth noting that this only becomes relevant once a public key is exposed, which typically happens when funds are spent, rather than applying uniformly across all Bitcoin wallets. A quantum computer can’t crack a public key it hasn’t seen.
But keep in mind that not all Bitcoin addresses are created equal when it comes to public key disclosure. Older P2PK outputs and Taproot (P2TR) addresses expose a public key on-chain as soon as funds are received. In contrast, legacy P2PKH and native SegWit P2WPKH addresses keep the public key hidden behind a hash until the moment the funds are spent.
Here at The Bitcoin Way, every client we set up runs on native SegWit addresses from day one. We never reuse an address, and Sparrow Wallet automatically routes any change to a fresh, never-before-used address. That combination already puts our clients in one of the strongest positions possible today when it comes to quantum resistance.
What Actually Changed
So the theoretical threat of quantum computers is nothing new.
What’s changed recently is that researchers are coming up with more optimistic theoretical models of the attack.
Google recently published a paper claiming they’ve found a more efficient way to model breaking elliptic curve cryptography. One of their estimates suggests that attacking Bitcoin’s keys could theoretically be done with around 1,200 logical qubits, which is a notable reduction from previous estimates.
This sounds impressive at first glance. But let’s be precise: this is still purely theoretical work. The paper doesn’t demonstrate an actual working attack. It doesn’t even publish the full quantum circuits. Instead, it offers a “zero-knowledge proof” that the concept could work mathematically.
That’s interesting on paper. It isn’t the same as showing it can be done in the real world. We are still nowhere near anyone being able to use a quantum computer to expose your private key.
So yes, the theoretical path looks a little clearer on the drawing board. But the actual machine required to walk that path still doesn’t exist.
Reality Check
Let’s look past the headlines and read what the paper actually says.
The estimates still rely heavily on assumptions about error rates, hardware stability, and system design; none of which have been achieved in real quantum systems. Change just one of these variables and the required resources can shift significantly.
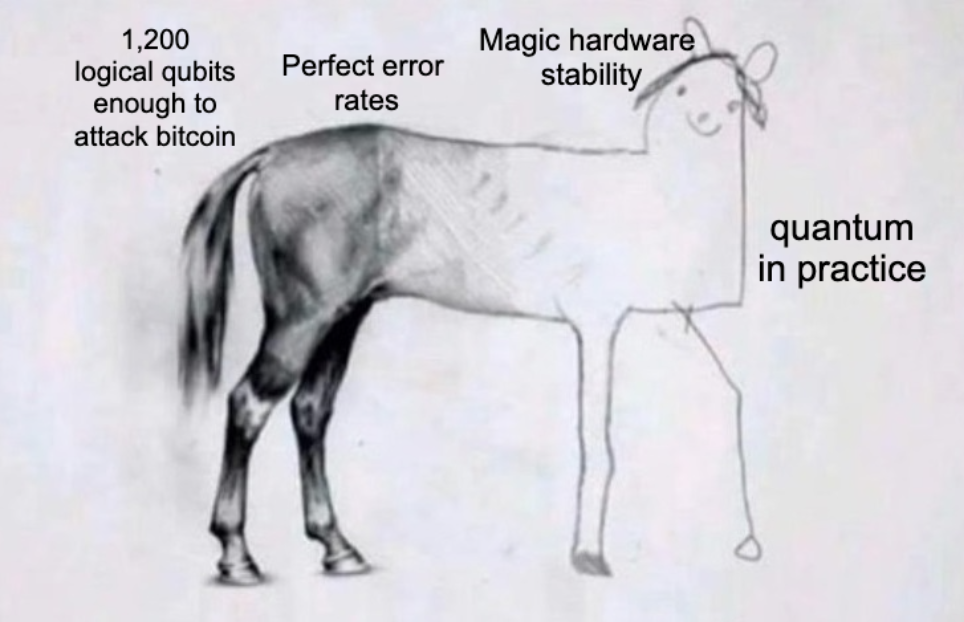
Error correction overhead is still enormous. Think of it like trying to take one clear, perfect photo, but your camera is so shaky that you need to take thousands of blurry shots just to stitch together one usable image. Today’s quantum systems have extremely high error rates, so you often need thousands of noisy physical qubits just to create one stable logical qubit.
Coherence time is a killer problem. Qubits lose their quantum state in fractions of a second. The estimates in the paper, by contrast, assume hundreds of thousands of physical qubits operating with sustained stability over much longer durations. Shor’s algorithm would require them to stay perfectly stable for much longer periods. It’s like trying to solve a long, delicate puzzle while someone keeps turning the lights off every few seconds.
When you compare this to current hardware, the gap becomes clearer. And the gap between those two realities isn’t incremental, it spans several orders of magnitude, in both scale and time.
It’s also worth noting the incentives at play. Google has major investments in both quantum hardware and post-quantum cryptography solutions. Plus, one of the co-authors is a researcher at the Ethereum Foundation because nothing says “objective research” like having someone from one of Bitcoin’s biggest competitors on the paper.

None of this invalidates the research. But it does help explain why the framing often leans toward urgency, even when the real-world timeline is still highly uncertain.
The end result is the usual confusion: A theoretical improvement starts to feel like an imminent breakthrough. A long-term risk gets sold as an immediate crisis. And that’s exactly where most of the noise comes from. But here’s what most people miss: Bitcoin developers aren’t sitting around waiting for a crisis. They’re already shipping.
Bitcoin Is Already Adapting
Bitcoin isn’t sitting around waiting for a crisis to hit.
Work on post-quantum security is already underway, not as a panicked reaction to headlines, but as a calm, long-term insurance policy to make sure the system can evolve if it ever needs to.
At a high level, this means moving away from signature schemes that rely on assumptions vulnerable to quantum attacks, and toward alternatives that remain secure even under those conditions.
For example, recent research has explored hash-based signature constructions designed specifically for Bitcoin’s constraints. One such proposal, referred to as SHRIMPS, focuses on making post-quantum signatures more practical by reducing their size and distributing responsibility across multiple devices.
Other approaches look at how transactions themselves are structured. For example, by not exposing public keys until the moment they’re spent.
One direction, referred to as the BIP 360 proposal, involves using Merkle-based constructions to commit to multiple possible spending paths upfront, allowing more flexible and secure conditions without exposing unnecessary information on-chain. This kind of structure can reduce the attack surface while remaining compatible with more advanced cryptographic schemes.
These ideas are not purely abstract. They are being actively researched, discussed, and in some cases implemented in controlled environments within the ecosystem, often over multi-year timeframes.
That slow, deliberate pace isn’t a bug. It’s a feature. Bitcoin’s upgrade process is intentionally conservative because the cost of getting it wrong is catastrophic. New primitives only get adopted once they’ve been thoroughly reviewed, heavily tested, and proven to behave reliably under real stress.
What this means in practice is that adaptation doesn’t happen suddenly. It happens gradually, at the edges, through research, experimentation, and incremental improvement.
This Isn’t a Bitcoin-Specific Problem
It’s also worth stepping back and looking at the bigger picture.
The media loves to frame quantum computing as a “Bitcoin-only problem”. They pretend that banks, payment networks, government databases, military systems, and even nuclear command-and-control infrastructure are magically immune.
Every paper or headline conveniently forgets to mention that the biggest targets would be the legacy financial system and classified networks that still run on ancient tech. Effectively, the systems that would actually face the most immediate and catastrophic risk are the centralized ones.

These are the same institutions that love to lecture everyone else about “systemic risk” while still running decades-old legacy infrastructure stacked like a Jenga tower. On paper they have one supposed advantage: they can issue decrees and force upgrades faster than Bitcoin’s deliberate process allows. But history shows that centralized power doesn’t magically translate into speed or competence.
One memo, one deadline, and supposedly everyone complies. Right?
Banks, payment rails, and government networks are often the most fragile precisely because they can force change from the top. When quantum eventually hits, they’ll rush the “fix”, declare victory, and quietly leave behind one forgotten server farm still running 1024-bit RSA because “it’s too expensive to touch” or “the old system is too complex to migrate fully”.
We’ve already seen this movie. Look at the U.S. federal courts’ CM/ECF system, which is the backbone for electronic case filings. It’s a glorious mess of 1990s and early 2000s technology, heavily customized by each court, held together with hope and duct tape.

Multiple times, including the 2020 SolarWinds breach and another nasty incident in 2025, foreign actors strolled right in and exploited exactly those legacy gaps. Even with top-down pressure from Washington to modernize, the upgrades were slow, uneven, and left plenty of vulnerable pockets behind. Because, surprise surprise, when you have decades of tangled legacy code and bureaucratic chains, “just issue a memo and upgrade” turns out to be a lot harder than it sounds on a PowerPoint slide.
Centralized power can order change quickly, but it usually ends up papering over cracks instead of fixing the foundation. Bitcoin is the opposite. It can’t print money to hide problems or force upgrades by decree. Every change has to earn real consensus from people who have skin in the game because their own money is sitting on the chain.

That deliberate slowness looks inefficient on the surface until a real threat appears. Then the incentives flip. Suddenly every node moves with real urgency. No endless committee meetings or legacy excuses. Just pure economic pressure.
That is the strongest coordination mechanism ever invented. Think about it, centralized systems can order change whereas Bitcoin, under the right circumstances, incentivizes it.
While You Worry About Quantum Your Seed Phrase Is Sitting in a Drawer
Which brings the focus back to something more immediate.
For most people, the risk to their Bitcoin isn’t some distant quantum supercomputer quietly plotting to take your coins. It comes from much simpler, far more common issues. Coins are lost every day because backups are incomplete, devices are compromised, or seed phrases are stored insecurely.
In many cases, due to a small oversight, something that seemed insignificant at the time but becomes irreversible later. These are not edge cases. They are the dominant failure modes today.
That’s what makes the long-term discussion around quantum both important and easy to misinterpret. Important, because it points to real changes that may eventually be required. But easy to misinterpret, because it shifts attention toward a sexy future threat while the actual risks today remain boringly simple, and far more immediate.
Even if the protocol evolves to address new cryptographic challenges, the nature of using Bitcoin securely is unlikely to become simpler.
In many cases, it moves in the opposite direction. More advanced security models, whether through multisig setups, distributed backups, or post-quantum schemes, tend to introduce more structure, more coordination, and more decisions for the user.

That’s where the real challenge sits. Not in a quantum computer lab or server center, but in the gap between what Bitcoin allows… and how people actually manage it in practice.
Security Isn’t a One-Time Decision
If reading this leaves you feeling clearer, but also slightly aware that securing Bitcoin may demand more from you over time, that’s a healthy reaction.
The goal isn’t to understand every proposal or keep up with every technical detail. Whether it’s something called SHRIMPS, BIP-360, or whatever comes next, most people won’t and don’t need to follow every development closely.
What matters is making sure your setup is robust enough for the world we already live in, while staying aligned with the direction Bitcoin is moving in.
That includes practical questions most people don’t revisit often enough, especially around how and when your public keys are exposed. If you’re worried about quantum, that detail becomes more than theoretical. Coins with publicly exposed keys are the ones that would be most directly affected, which makes address types, spending patterns, and key management part of a longer-term security posture.
It also includes how your backups are structured, how access is distributed, and how your setup would hold up under different scenarios.
You don’t need to figure all of this out alone.
If you’d like help reviewing your setup, thinking through your custody structure, or making sure you’re positioned for what’s ahead, including how to minimize unnecessary public key exposure, you can book a free 30-minute consultation.
We’ll help you find a solution that works best for you.
