7 Bitcoin Privacy Tools You Should Be Using in 2026

In this article:
As financial surveillance gets more widespread, protecting your Bitcoin privacy becomes critical.
Many people still think that blockchain transactions are anonymous, but they’re actually pseudonymous, which means every transaction leaves a public trail that can be traced back to the sender.
Luckily, a range of Bitcoin privacy tools now exist to address this. They help you buy, sell, store, and manage your bitcoin more privately, limiting what others can learn about your identity and activity.
Key Takeaways
- Without privacy tools, blockchain transactions leave a traceable public record.
- Layering protections (privacy wallets, collaborative transaction tools, VPN, Tor, encrypted communications, and hardware security keys) strengthens your defense against surveillance.
- Bitcoin privacy tools shield your transaction history and identity, reducing your risk of targeted attacks and preserving your financial autonomy.
Why Do You Need Bitcoin Privacy Tools?
Bitcoin privacy tools are necessary for several reasons.
Blockchain Transparency
For all the good it brings (like enabling trustless verification), transparency on the blockchain has its caveats. If someone finds out just one of your wallet addresses, they can see its activity and use common heuristics to infer related addresses.
Financial Surveillance
With bitcoin entering mainstream finance, compliance monitoring and blockchain analytics have ramped up in many jurisdictions. This puts growing pressure on individuals’ right to financial privacy.
Personal Security Risks
Keeping your bitcoin holdings private is important for your physical security. If someone with bad intentions finds out how much BTC you hold, you can become a target of theft, extortion, or even physical attacks.
Protecting Your Sovereignty
The thought of people (government, institutions, criminals) snooping around your wallet is a danger to your financial sovereignty. Without good privacy and security practices, your funds can be frozen, flagged, seized, restricted (on custodial platforms), or lost due to coercion and scams.

7 Bitcoin Privacy Tools You Should Consider Using
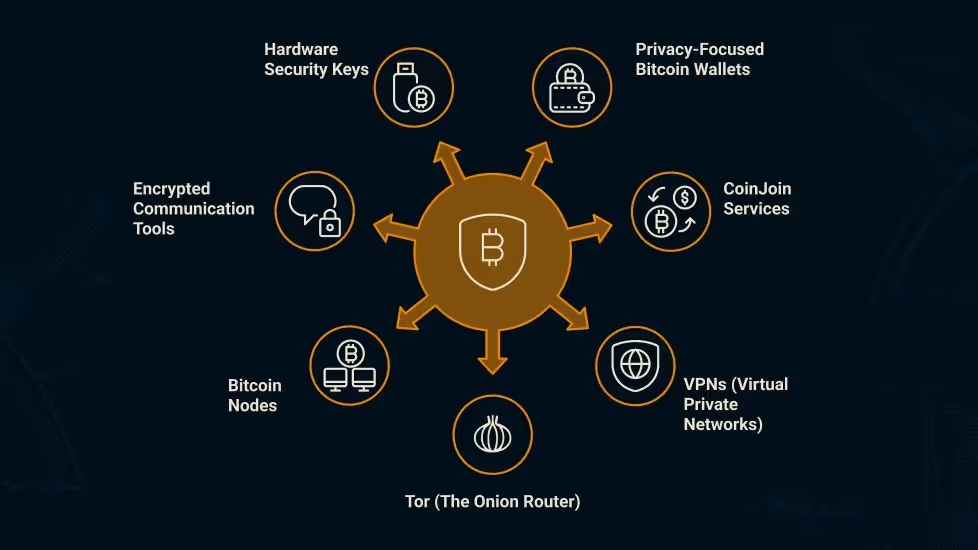
To reclaim your privacy and protect yourself and your assets, there are several tools you can use, either on their own or (selectively) combined.
Privacy-Focused Bitcoin Wallets
Privacy-focused bitcoin wallets can hide your transaction history and prevent addresses from being linked to each other. They also don't require KYC, unlike many custodial wallets and services.
Key Features To Look For
A privacy wallet should have coin control (UTXO management), support for collaborative transaction protocols like CoinJoin or PayJoin, Tor integration, and, obviously, no KYC requirements.
Best Practice
Use a privacy wallet for most transactions. Transacting from cold storage can reveal how much bitcoin you hold.
CoinJoin
CoinJoin tools join your bitcoin with other users’ coins. This obscures the link between sender and receiver, making transactions harder to trace (even if you bought coins on a KYC platform).
Key Features to Look for
Look for CoinJoin tools that are non-custodial (no one but you controls your funds) and clearly explain what privacy guarantees they do and don't provide.
Best Practice
CoinJoin works best for coins you plan to spend directly. Depositing ‘joined’ coins back to exchanges can draw regulatory scrutiny. Keep in mind that employing these services can increase your fees.
VPNs (Virtual Private Networks)
VPNs encrypt your internet traffic and mask your IP address. Without one, the services you connect to and your internet service provider can log your activity and approximate location when you connect to nodes, exchanges, and wallets.
Key Features To Look For
The best VPNs for bitcoin users have a strict no-logs policy, accept bitcoin payments, are based in privacy-friendly jurisdictions, and offer a kill switch that cuts your internet connection if the VPN protection drops.
Best Practice
Use a VPN on public Wi-Fi or any other untrusted network.
Tor (The Onion Router)
Tor is a decentralized network that routes your internet traffic through multiple encrypted layers (hence the “onion” name) to hide your IP address. It works much like a VPN, but instead of trusting a single provider, you relay traffic through independent nodes, so no single party can see the full picture.
Key Features To Look For
Look for wallets with native Tor integration and support for .onion addresses. The ability to run your own node over Tor and automatic traffic routing without manual setup are also important.
Best Practice
Route your Bitcoin node traffic over Tor to reduce the chance of your IP being correlated with your transactions.
Bitcoin Nodes
Running your own Bitcoin node lets you validate and relay transactions without third parties. Without one, your wallet connects to someone else's server, which can reveal the addresses and transactions you query and link that activity to your IP.
Key Features To Look For
Your node should be fully under your control, self-hosted, running on reliable hardware, have good uptime, regularly updated, features safe key management, and supports different implementations. Dedicated devices like Start9 or Umbrel make setup easier but are optional.
Best Practice
Run your own full Bitcoin node to verify transactions independently and keep your wallet activity private.
Encrypted Communication Tools
Some communication tools use end-to-end encryption, which ensures no one other than you and the recipient can read your messages. If you discuss bitcoin holdings or transactions over unencrypted channels, you risk having that information intercepted and used for social engineering attacks.
Key Features To Look For
Look for tools that collect minimal metadata, are open-source, and have passed independent audits. Note that the phone number requirement is a privacy trade-off.
Best Practice
Never discuss your bitcoin holdings or transactions over unencrypted SMS, email, social media, or messaging apps.
Hardware Security Keys
Hardware security keys are physical devices used for two-factor authentication (2FA). Unlike SMS-based 2FA, which is vulnerable to SIM swap attacks and phishing, hardware keys use cryptographic authentication (FIDO2/WebAuthn) that can't be intercepted remotely.
Key Features To Look For
Look for FIDO2/WebAuthn support, phishing-resistant authentication, PIN-protected access, and multi-account compatibility.
Best Practice
Use hardware security keys for every account tied to your bitcoin, including exchanges, emails, and password managers.
Enhance Your Bitcoin Privacy With The Bitcoin Way
The tools we’ve discussed form the foundation of strong bitcoin privacy. Start with a privacy-enhancing wallet and your own node, add CoinJoin and a VPN or Tor for transactions, secure your accounts with hardware keys, and use encrypted communication tools.
FAQs
What are the best tools for Bitcoin privacy?
The best tools include privacy wallets, collaborative transaction protocols, VPNs, Tor, your own Bitcoin node, encrypted communication apps, and hardware security keys. Using them together provides stronger protection against surveillance than any single tool alone.
Can I make my BTC untraceable?
There's no way to make bitcoin completely untraceable, but you can significantly reduce how much of your activity is visible. Combining tools like privacy wallets, Tor, and collaborative transaction protocols makes it much harder for anyone to trace transactions back to you.
