Bitcoin Is Secure. You Might Not Be.
In this article:
You secured your Bitcoin. Solid. But who secured the data about you?
In the first 3.5 months of 2026, 41 Bitcoin and crypto holders were kidnapped in France. One targeted snatch every 2.5 days. Pavel Durov, founder of Telegram, looked at the numbers and basically said out loud what everyone was thinking: why the hell is this exploding now?
Around the same time, a French tax official was accused of selling confidential data on cryptocurrency investors to criminal networks.

Shocking really. A government insider monetising citizen data for cash. Who could’ve predicted that from the same people who can’t balance a budget but love tracking every sat you own?
The connection doesn’t need speculation or tinfoil hats. This is exactly how professional targeting works in the real world. Not blurry guesswork but clean, structured intel that glues your real name, real address, and real Bitcoin holdings together. Tax records, exchange KYC dumps, all those lovely mandatory reporting systems. Once this data gets aggregated (and it always does), it doesn’t stay politely contained in some “secure” database.
It leaks. It gets sold. It ends up in the hands of people who don’t give a damn about your airgapped set-up.
You don’t need the complete customer database of every exchange in Europe. You just need enough reliable scraps to narrow the field, confirm the target actually holds real Bitcoin (not ETF paper promises), and decide the payout justifies the risk.
These were not random acts of violence. The victims appear to have been selected on the belief that they held Bitcoin, with attackers in some cases acting on prior knowledge of who they were targeting and where they could be found.
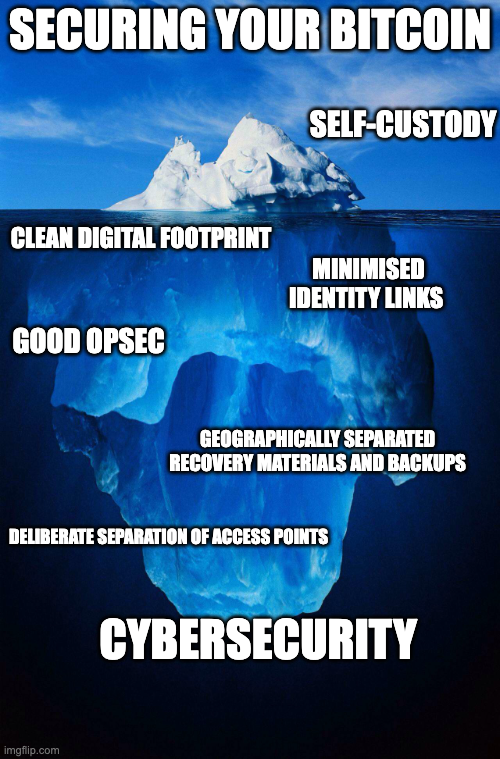
For years, you have likely treated Bitcoin security as a technical problem. Protect the keys, secure the device, stay offline. The risk of physical coercion has always been there, but in practice it is often treated as a remote edge case rather than something that shapes how you structure your setup.

What is now emerging in France challenges that assumption by shifting the focus from access to identification.
Bitcoin itself is still working exactly as designed. Your sats are safe behind proper self-custody. But the data trail pointing back to you? That’s the part the system never promised to protect, and the part governments and opportunists are increasingly exploiting. This is uncomfortable, but it’s also a loud signal. Self-custody was always just the starting line. Real sovereignty means thinking one layer deeper.
Why France? Follow the Exposure
France isn’t unique because of Bitcoin adoption. It stands out because it’s sitting smack on the front line of a much bigger shift in how governments are hoovering up and sharing financial information.
At the European level, this shift is being formalised. Frameworks such as DAC8 require crypto service providers to report detailed user data to tax authorities, which can then be exchanged across jurisdictions. This aligns with the Crypto-Asset Reporting Framework, extending the same model globally.

The direction is dead obvious: more data collected, more standardized, more shared. The system isn’t just peeking at your finances anymore. It’s building a structured, searchable map of who holds what. We discussed this dynamic recently in Sovereignty Doesn’t End at Self-Custody.
What France shows is what happens when that visibility reaches a certain density.
Because once enough information exists, the question is no longer whether someone can identify Bitcoin holders. It is how easily that identification can be acted upon. This is where the distinction between securing your Bitcoin and exposing yourself becomes unavoidable.

When Ledger suffered a data breach, no private keys were compromised. What was exposed were names, addresses, and contact details of people who had taken steps to secure their Bitcoin.
That information didn’t stay inert. It was circulated, traded, and used. Victims reported phishing campaigns, extortion attempts, and, in some cases, credible threats delivered directly to their homes. The breach did not compromise their wallets. It compromised their anonymity.

It drove home a simple but annoying reality: you can eliminate every technical vulnerability, run the tightest cold storage setup imaginable, and still be completely exposed at the identity layer.
France is where these dynamics have begun to converge. Structured data, expanding visibility, and actors willing to act on it.
From Data to Doorstep
The gap between information and action is smaller than most people assume.
Once a name can be linked to Bitcoin ownership, the rest doesn’t require sophisticated infrastructure. A dataset narrows a list. Location data confirms proximity. Public records, social media, and basic observation fill in the remaining gaps. What begins as partial information becomes a working profile.
Bitcoin holders are uniquely exposed once they become identifiable.
Think about it. A house? Massive paper wealth, but good luck converting that under pressure; you’re looking at time, lawyers, paperwork, and finding a buyer who isn’t spooked. Stocks? Tied up in regulated markets with brokers, trading hours, and systems that can halt or reverse everything on a whim. Bank accounts can be frozen or flagged instantly. Even gold isn’t exactly easy to move in meaningful amounts when the clock is ticking.
In each case, there is friction. That friction slows down extraction, introduces uncertainty, and creates opportunities for intervention.
Bitcoin is different.

If access can be obtained, value can be transferred directly, settled irreversibly, and moved beyond reach within minutes. There is no dependency on an institution, no approval process, and no mechanism to reverse the transaction once it is confirmed.
Those exact properties are what make Bitcoin the ultimate tool for sovereignty. You control it. No bank, no broker, no government middleman can block, delay, or censor your transaction. The network does exactly what the keys instruct it to do. That is what makes it powerful.
It also means that security doesn’t depend on anyone else. Responsibility sits entirely with the holder. There is no intermediary to question a transfer, no authority to pause it, and no process to recover funds after the fact. Once access is compromised, there is no external layer to step in. Bitcoin doesn’t distinguish between calm-day use and high-pressure extraction. It just settles.This efficiency is why Bitcoin is antifragile and why it terrifies the half-evil, half-incompetent clowns running the fiat system.

Your self-custodied Bitcoin is still the safest, most sovereign asset on the planet. The solution isn’t to fear Bitcoin or go back to the fiat world. The solution is to get serious about the layer around your Bitcoin: shrinking your data footprint, managing visibility, and building operational security that keeps the spotlight off you.
The Illusion of “I’m Too Small to Matter”
At this point, the natural reaction is to dismiss the risk.
“Nah, that happens to the big fish. I’m not a whale. I’m not flashing Lambos on Instagram. This kind of heat is for public figures and seven-figure stackers”.
Targeting doesn’t require exceptional wealth. It requires a combination of three conditions: identifiability, accessibility, and a credible expectation of value. Once those are met, the threshold for action is lower than most people expect.
In practice, mid-level holders can be more attractive than very large ones. They are less likely to have sophisticated protection, less likely to operate with anonymity in mind, and easier to approach without drawing attention. Often still thinking like fiat people while leaving breadcrumbs everywhere.

Data changes the economics of selection. Attackers can slice the list by location, lifestyle signals, past exchange activity, social media slips, or leaked tax records. They’re not hunting the global richest anymore. They’re hunting the easiest viable targets inside a narrowed group.
You don’t need to stand out globally. You only need to stand out within a narrowed set.
Practical Ways to Reduce Your Exposure
If this leaves you a bit uncomfortable, good. That feeling is justified. Not because the sky is falling, far from it. But because it’s forcing a real shift in how you need to think about securing your Bitcoin.
It means thinking about what information exists about you, where it sits, and how easily it can be connected. It means recognizing that exposure is rarely the result of a single mistake, but of small, accumulated signals that, over time, make you easier to identify.

Here are five practical steps you can start taking today
1. Audit and Reduce Your Digital Footprint
Most targeting begins with information that is already available. Search engines, old posts, forum activity, and leaked datasets can be combined into a profile without your awareness. What feels insignificant in isolation becomes meaningful when aggregated.
Take the time to understand what exists about you. Remove what you can, restrict what you control, and avoid creating new links between your identity and Bitcoin activity. Going forward, separation should be deliberate rather than incidental.
2. Avoid Creating Obvious Wealth Signals
You don’t need to mention Bitcoin for people to form conclusions. Visible changes in lifestyle, especially when they coincide with market cycles, can create a credible signal of accessible wealth. In practice, this is often enough. Maintaining a low profile isn’t about hiding success. It is about avoiding patterns that make you easier to single out relative to those around you.

3. Limit Who Knows What You Hold
Information spreads most efficiently through people. Even casual conversations can create a chain of knowledge that moves beyond your control. Over time, that chain becomes difficult to trace and impossible to retract. A simple rule is effective: do not disclose holdings, balances, or setup details. Where disclosure is necessary, keep it limited and intentional.

4. Structure Access: Decoy and Distribution
The way your Bitcoin is structured determines what happens under pressure.
If everything can be accessed from a single device, location, or interaction, then the entire balance is effectively exposed once that point is compromised. A more resilient approach separates access.
This typically involves maintaining a smaller, accessible wallet with a believable balance that can be disclosed if necessary, while the majority of funds are stored separately in locations that are not immediately reachable. Recovery materials and access paths should not be concentrated in one place, and ideally not even in one geographic area. The objective is to ensure that no single moment of coercion results in full loss.

5. Control Future Data and Personal Security
You cannot erase all past exposure, but you can reduce what you add from this point forward.
Be deliberate about where you create accounts, how often you go through KYC processes, and how tightly your identity is linked to your Bitcoin activity. Fewer connections mean fewer opportunities for that information to be accessed or misused.
Where possible and legally available in your jurisdiction, prefer non-custodial, low-KYC or no-KYC peer-to-peer methods for on-ramps and off-ramps. Review existing exchange and brokerage accounts, and request data minimization or deletion of non-essential records where regulations permit. For any remaining fiat flows, use dedicated, privacy-oriented accounts rather than mixing them with your primary financial activity.
At the same time, consider your physical security in a practical way. That includes awareness of routines, limiting predictable patterns, and, where appropriate and legal, personal protection measures.

Don’t Become the Easy Target
France isn’t the exception. It is a warning.
The same ingredients exist everywhere: mandatory reporting, exchange KYC, expanding tax frameworks, data brokers, social media, leaked databases, and people who underestimate how much of their life is already searchable.
Bitcoin isn’t the problem. Bitcoin is doing exactly what it was designed to do. It gives you control over wealth without asking permission from a bank, broker, custodian, or government middleman. That is why it matters, why it works, and why we use it.
If your Bitcoin is properly self-custodied but your identity, habits, access points, and recovery setup are still easy to map… then you’ve only solved half the problem. You hold the keys, but the entire layer around those keys still needs serious work.
The goal isn’t to become a paranoid ghost living off-grid. The goal is simpler and more powerful: become a harder target.
Harder to identify. Harder to assess. Harder to pressure. Harder to compromise. Fortunately, you do not need to figure this out alone.
At The Bitcoin Way, we help clients build serious Bitcoin self-custody setups without unnecessary complexity. That means securing your Bitcoin properly, reducing avoidable exposure, improving privacy, structuring access, and making sure your sovereignty works in the real world, not just in theory.
If you want to understand where your current setup is strong, where it is exposed, and what you should fix first, book a free 30-minute consultation with our advisors.
Because Bitcoin gives you freedom. Your setup determines whether you can keep it.
